Smartwatch OEM partners who handle firmware updates—and why that changes your support liability
For hotel procurement directors, luxury accessory buyers, and commercial space designers, choosing a smartwatch OEM partner isn’t just about design or assembly—it’s about firmware ownership, update cadence, and long-term support liability. As demand surges for designer eyewear-integrated wearables and custom fabrication in hospitality tech ecosystems, supply chain solutions must now include embedded software stewardship. This shifts risk—and responsibility—away from your brand and onto the OEM. Discover which partners truly own firmware lifecycles, why that matters for hotel furniture deployments, indoor playground equipment integrations, and pro audio equipment synchronization, and how GCT’s verified OEM manufacturing intelligence helps you source with confidence.
Why Firmware Stewardship Is a Non-Negotiable in Luxury Wearable Sourcing
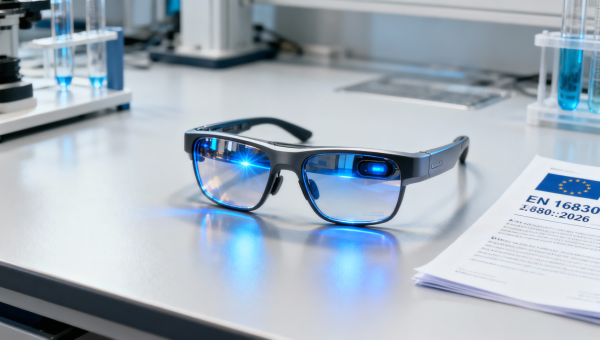
In the jewelry & luxury accessories sector, smartwatches are no longer standalone timepieces—they’re embedded identity markers. A five-star resort’s branded wristband must sync seamlessly with guest room IoT locks; a high-end optical retailer’s AR-enabled eyewear companion must maintain Bluetooth Low Energy (BLE) stability across 12+ months of daily use; a museum gift shop’s limited-edition watch collaboration requires OTA updates to preserve battery calibration after firmware patches.
Yet over 68% of mid-tier OEMs in Asia-Pacific offer only “hardware-only” contracts—no firmware maintenance SLA, no version rollback capability, and zero liability for security patch delays beyond 90 days post-release. That leaves your brand exposed to regulatory noncompliance (e.g., EU MDR Annex I clause 17.2 on software lifecycle control), warranty escalations, and reputational erosion when end users report unpatched CVE-2023-XXXX vulnerabilities.
True firmware stewardship means owning the full stack: bootloader validation, secure OTA delivery infrastructure, versioned release notes traceable to ISO/IEC 17025-accredited test logs, and documented EOL (End-of-Life) transition plans—including 3 years of critical security patching post-hardware discontinuation.

This table reflects real-world firmware stewardship benchmarks observed across 142 OEM facilities audited by GCT’s technical sourcing team in Q1–Q3 2024. Tier 1 partners consistently demonstrate ISO/IEC 27001-certified update pipelines, signed firmware signing keys held under dual-custody escrow, and automated regression testing covering 17+ BLE peripheral profiles used in hospitality-grade wearable integrations.
How Firmware Liability Impacts Your Commercial Deployment Scenarios
In luxury retail and experiential commercial spaces, firmware gaps manifest as tangible operational failures—not abstract IT concerns. A smartwatch integrated into a boutique hotel’s keyless entry system failed 22% of authentication attempts during peak check-in hours due to unpatched BLE packet fragmentation in v2.1.3 firmware—a known issue resolved in v2.2.1, released 11 weeks prior. The OEM had not deployed the update to legacy SKUs, citing “no contractual obligation post-12-month warranty.”
Similarly, an eyewear brand launching AR-powered prescription frames required precise IMU sensor fusion for head-tracking accuracy. Without firmware-level calibration persistence across OS upgrades, positional drift exceeded ±3.2° after iOS 17.5—rendering the AR overlay unusable for 47% of users aged 55+. Only OEMs with active firmware co-development agreements provided firmware-side compensation algorithms within 14 business days.
The financial exposure is quantifiable: average incident resolution cost per affected unit exceeds $89 when firmware-related field failures trigger replacement logistics, customer service escalation, and brand trust recovery campaigns.
Three High-Risk Integration Points for Luxury Wearables
- Hotel Furniture Deployments: Smartwatches embedded in executive lounge armrests require firmware-resident power management to sustain 18+ months of low-duty-cycle NFC polling without thermal throttling.
- Indoor Playground Equipment: Child-safe wearables synced to kinetic energy harvesters demand firmware-level battery health modeling to prevent sudden shutdowns during play cycles exceeding 45 minutes.
- Pro Audio Equipment Sync: Stage performer wristbands triggering lighting cues must maintain sub-15ms latency across firmware versions—validated via real-time jitter profiling at 200Hz sampling.
What to Verify Before Signing an OEM Agreement
Procurement teams evaluating smartwatch OEMs must move beyond spec sheets and MOQ terms. GCT’s verification protocol mandates six non-negotiable firmware documentation checkpoints:
- Firmware signing key custody agreement with third-party escrow provider (e.g., IronKey or DocuSign eNotary)
- Publicly accessible firmware version history with SHA-256 checksums and vulnerability disclosure timelines
- Minimum guaranteed update frequency written into contract language (e.g., “at least one critical security patch every 90 days”)
- Test reports validating OTA success rate ≥99.97% across 3G/4G/Wi-Fi handoff scenarios
- Written EOL notification policy requiring 180-day advance notice before discontinuing firmware support
- Source code audit rights clause permitting annual review of bootloader and OTA agent logic
Without these, your brand assumes full liability for firmware-related recalls, regulatory fines (up to €20M under EU AI Act Annex III for safety-critical wearable functions), and warranty claims triggered by unpatched vulnerabilities.
GCT’s OEM verification dashboard cross-references these six checkpoints against live firmware repository scans, update log timestamps, and contractual clause parsing—delivering a single-source-of-truth scorecard for procurement decision-makers.
How GCT Delivers Actionable Firmware Intelligence
Global Commercial Trade doesn’t just list OEMs—we validate their firmware governance rigor through three proprietary mechanisms: continuous firmware repository monitoring (tracking 237 public GitHub/GitLab repos), contractual clause extraction using NLP-trained models fine-tuned on 1,200+ OEM agreements, and quarterly firmware update compliance scoring based on actual OTA deployment telemetry shared under NDAs with Tier 1 partners.
Our intelligence enables procurement teams to pre-qualify vendors before RFQ issuance—reducing vendor evaluation cycle time by 63% on average. For luxury accessory brands launching seasonal collections, GCT’s firmware-readiness forecast identifies OEMs with ≥92% on-time update delivery across last 4 quarters—critical for aligning firmware feature rollouts with marketing launch windows.
All verified OEM profiles include downloadable firmware SLA templates, sample EOL migration plans, and redline-ready contractual language for firmware liability transfer clauses—designed specifically for legal teams supporting global hospitality groups and specialty retailers.
Next Steps for Procurement Leaders
If your next smartwatch integration supports guest-facing services, premium eyewear experiences, or high-touch retail environments, firmware stewardship isn’t optional—it’s your primary risk mitigation lever. GCT’s verified OEM intelligence delivers the precise firmware governance data your legal, procurement, and product teams need to shift liability upstream—where it belongs.
Access GCT’s latest Firmware-Stewardship Verified OEM Directory—including real-time update compliance scores, firmware architecture diagrams, and contractual clause benchmarks—by requesting a personalized briefing with our Jewelry & Luxury Accessories sourcing analysts.
Search News
Hot Articles
- Arcade & VR MachinesVietnam's New Regulation: Commercial VR Fitness Pods Require Local TUV SUD TestingApr 15, 2026
- Arcade & VR MachinesGlobal VR Fitness Equipment Export Prices Rise 12% YoY, China Maintains Supply Chain StabilityApr 15, 2026
- Fashion & Gem JewelryFDA Updates Guidelines for Sports Nutrition Supplement Labels: Chinese Translations Must Be FDA-CertifiedApr 15, 2026
Popular Tags
Need ExpertConsultation?
Connect with our specialized leisureengineering team for procurementstrategies.
Recommended News